The global AI cybersecurity market went from (current) $25.35 billion in 2024. It is expected to reach around $93.75 billion in 2030 showing how quickly website security has turned into a digital arms race. Today, cyber threats are not merely byproducts of a hacker’s garage, in fact attackers now employ machine learning to speed up attacks. They also create hyper realistic phishing campaigns and discover vulnerabilities more rapidly than human teams can deploy patches. AI-driven cyberattacks have already affected 74% of IT security experts. This shows that advanced security is now an urgent requirement, not something to worry about later.
Because of this, hosting providers now build AI directly into their infrastructure. These systems run behavioral analytics in real time and isolate threats within milliseconds. What once cost a fortune and took years to develop has now become a baseline expectation; this has now become an easy expectation. Cyberattacks continue to grow in sophistication. This blog explains how hosting platforms like UltaHost fight these threats. It covers anomaly detection, DDoS protection, malware scanning, and predictive threat intelligence.
Key Takeaways
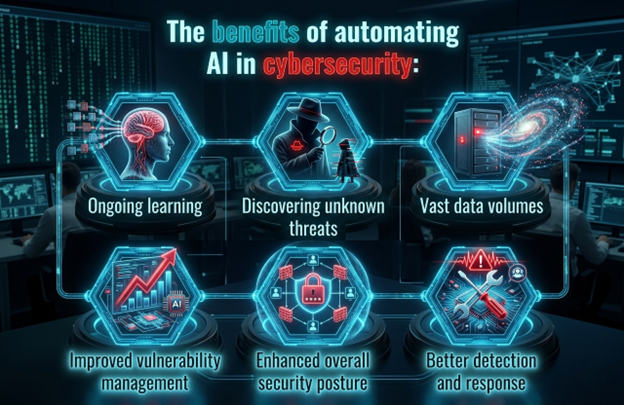
- Machine learning has transformed cybersecurity to proactive as opposed to reactive defense. Hosting providers are now able to spot suspicious activity. This assists in preventing unknown or zero day threats before they create damages.
- AI driven DDoS protection has become essential, as ML models can accurately separate real traffic from attack floods, something traditional rate-limiting rules simply can’t do.
- The new security is now concerned with behavioral malware detection. Process monitoring assists to detect polymorphic and fileless attacks. These threats are not detected by traditional antivirus tools.
- Hosting security is changing due to predictive threat intelligence. It integrates internal information with worldwide threat intelligence. This assists providers to predict attacks rather than respond to attacks occurring.
- Alternatively, to be actually security oriented, hosting has to be infrastructure committed. There should be defense at all levels. This is aided by constant monitoring, patching, and professional supervision.
| Many providers will tout security add ons, but you want to look for platforms where protection is at the server, network and authentication levels. Security, after all, is best when it’s integrated into the architecture and not an afterthought. |
Don’t wait for cyber threats to disrupt your business.
Secure your website with UltaHost’s AI powered hosting built with real time protection, DDoS defense, and proactive threat monitoring.
How Machine Learning Powers Real Time Threat Detection
There was an inability to block the known threats with the use of early signature based detection systems. Once attackers changed their techniques, these systems quickly lost their value. Machine learning enhances security by analysis of behavior. These systems identify abnormal activity instead of relying on old threat patterns. Normal network and user behavior is first learned by AI. It is then able to identify real time anomalies. Such examples are the strange logins or the access to sensitive information without permission.
- Unsupervised learning models, such as isolation forests and autoencoders, can detect anomalies without needing past attack examples, which helps identify unknown threats early.
- Supervised models train on labeled threat datasets. These datasets define traffic as malicious or safe. Such tools as Symantec TAA constantly monitor the behavior of the network and send alerts about the problems emerging.
- Detection is also enhanced by deep learning neural network solutions. Sophos Intercept X can be used to monitor endpoint behavior as an example. It detects signs of compromise without the use of central database of threats.
In short, the speed advantage is revolutionary. Thousands of logs can be analyzed by human analysts daily. Millions of events can be analyzed using ML models per second. Automation is needed in hosting companies that are dealing with massive infrastructure.
DDoS Mitigation: Training Machines to Tell Traffic from Attacks
One of the biggest threats to the hosting infrastructure is DDoS attacks. They complicate the process of distinguishing between healthy traffic spurts and malicious floods. Conventional rule-based defenses can frequently have a hard time when there is overlap in traffic patterns. The modification of machine learning is that it would analyse behaviour rather than merely depending on quantity thresholds. ML systems process a number of signals in real time. This assists the hosting providers to identify true visitors and coordinated botnet activity.
Modern ML driven DDoS mitigation achieves this through several intelligent techniques:
- This technique is effective against botnet traffic. It examines various indicators such as packet timing, request types, IP reputation and geolocation. These indicators show unnatural traffic patterns.
- Reinforcement learning models that persistently adapt the defense strategies and automatically improve filtering rules based on past attack results.
- Clustering algorithms that take clustering algorithms group suspicious requests into behavioral segments, blocking malicious cohorts while allowing legitimate visitors unfettered access.
- Models dedicated to predicting traffic which catch even abnormal spikes early on and enable systems to scale resources or trip defenses before the disruption arrives.

| Traffic spikes can be indistinguishable from attacks but intelligent mitigation ensures that valid visitors remain connected while malicious traffic is screened automatically. As a result, it means intelligent DDoS protection directly protects uptime, revenue and user trust. |
Malware Detection and Behavioral Analysis: Beyond Signature Scanning
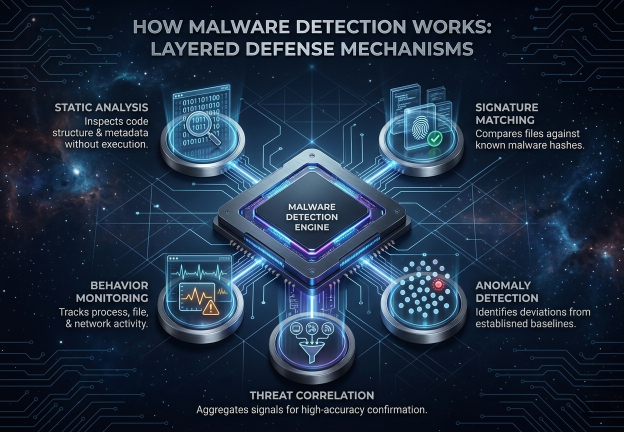
The signature-based scanners countered initial malware. These scanners are usually by-passed by modern dangers. Metamorphic, polymorphic and fileless malware are always improving or never use files at all. As a result, hosting environments now rely on machine learning based behavior analysis which identifies threats by how it acts rather than its code appearance. In one instance, a process can just randomly access sensitive files. It can also strive to reach closed servers. Even when the malware is novel, ML systems are able to indicate this behavior as malicious.
- Deep learning plays an important role in static analysis, where deep learning models scan structural and bytecode patterns of executables before they ever run, catching evasive malware before execution.
- Dynamic analysis executes suspicious code within sandbox environments. These separated systems enable security personnel to track behavior in a secure manner. Live infrastructure is secured.
- The memory forensics models trace the process injection attacks and the hollowing attacks. They acquire other fileless methods as well. These threats are usually overlooked by the traditional scanners.
| Threats can be detected by AI at the speed of technology, but humans are still needed to investigate and make decisions. So, the most secure hosting environments are those that use automation while maintaining continuous expert oversight. |
Predictive Threat Intelligence: Staying Ahead of Attacks Before They Happen
Unlike reactive security that occurs when a threat comes into being, predictive threat intelligence employs machine learning algorithms to forecast an attack before it occurs. These models are real-time risk scoring models. They integrate server logs, traffic patterns and vulnerability data. They also utilize external intelligence like CVE alerts and malicious IP activity. This means that the hosting providers will have the ability to deploy security beforehand and make cybersecurity more of a proactive measure instead of reaction.
- Natural language processing (NLP) models analyze dark web forums, security bulletins, and threat reports to extract indicators of new attacks and turn unstructured text into useful risk intelligence.
- Graph neural networks have the potential to assign new attacks to established threat groups and forecast their future victims by mapping the links between malicious actors, infrastructure and attack campaigns.
- Vulnerability prioritization models rank unpatched vulnerabilities according to their real world likelihood of exploit in the wild, allowing teams to target patching efforts where it is most useful rather than attempting simultaneous patching of everything.
Unlike reactive security, which responds after an attack commences, predictive threat intelligence aims to halt threats early. Machine learning is real-time, connecting external cues like vulnerability notifications and malicious IP traffic with internal server data, which allows identifying the increasing threats. This allows hosting providers to respond earlier before it is too late, and provide a more proactive security response rather than reactive response which is usually too late.

How UltaHost Builds Intelligent Security Into Its Hosting Infrastructure
In the case of hosting security, the actual contrast is between hosts who add security on afterward and those who work it into infrastructure, this is the place UltaHost succeeds. Powered by SuperMicro hardware and AMD EPYC processors, 30+ global data centers help the platform achieve continuous ML based security monitoring without sacrificing performance. Plus, its integration of Monarx behavioral malware protection allows real time threat detection through script activity examination or against the signature-based scanning that housed itself at the level of infrastructure rather than sitting in front of live traffic.
- All plans include DDoS protection, and intelligent traffic analysis can discern volumetric attack floods from legitimate traffic spikes without manual intervention.
- Web gateways scan traffic between client devices and application servers at the application layer. By doing so, they can prevent injection attacks, cross-site scripting, or any other OWASP Top 10 threat before the request ever gets to the application code.
- The platform is able to match the behavioral indicators, including time of login, IP positioning, and fingerprinting of devices, to identify suspicious authentication requests and send live notifications in advance, before unauthorized sessions can even start.
- BitNinja (free with VPS and dedicated hosting plans), adds a multi-layered defense stack consisting of log analysis, honeypots, and IP reputation management which gives behavioral information back to a network-wide threat intelligence pool.
It’s not just the features that makes UltaHost secure, but rather its way of business. The platform utilizes firmware updates and security patches, one of the most effective measures against conventional entry points of an attack, to harden its infrastructure.
The Human AI Balance: Why Automation Alone Isn’t Enough
Contemporary security relies on smart systems. Such systems identify threats at a quicker rate. They react to DDoS attacks better and detect suspicious activity at an early stage. The best model for security, therefore is a hybrid human machine security model, where the work of machine learning can analyse large amounts of data to react in minutes if not seconds to an imminent attack but leave the judgment, investigation advance level threat detection and strategic planning to humans avoiding the temptation of blind automation which has proved almost universally unreliable.
The sector is currently crafting more precise AI incident response principles because organizations have realized that the breakdown of AI systems merits varying playbooks.
Organizations that apply AI with appropriate human oversight and governance frameworks have MTTD and MTTR many times lower than the fully manual or fully automated alternatives.
All AI security decisions should produce full audit logs for human analysts to review.
Security teams now treat routine red team exercises for AI systems as standard practice. The tests are adversarial manipulation, model evasion, and false negative tests.
Treat Host Security as Risk Management and not a Check List.
In the context of cybersecurity, it is not the longest list of features that a specific host is best but one that keeps on updating the infrastructure, inspecting activities and predicting attacks. Concisely, long-term resilience versus short-term convenience.

Upgrade to UltaHost today
Experience hosting designed for modern cyber threats, performance, and continuous security.
Final Thoughts
The cyber threats are dynamic and the concept of hosting security has long since gone well beyond the traditional, rule based defense. Modern security depends on intelligent systems. These systems detect threats faster. They respond to DDoS attacks more accurately and identify suspicious activity early. Nevertheless, technology is not sufficient in itself. AI-enhanced automation plus resilient infrastructure, disciplined operations, and human supervision are the best security measures. Secure hosting is no longer a nice-to-have product in case of modern businesses. It is an element of digital resilience. This is why such providers as UltaHost pay attention to the idea of developing security as the part of their infrastructure, which enables websites to remain secure when threats become more sophisticated.
FAQs
What makes machine learning better than traditional threat detection?
Unlike traditional tools that rely on known attack signatures, machine learning focuses on behavioral patterns. Therefore, it can detect zero-day exploits, unusual login activity, and emerging threats that bypass conventional security methods.
How does AI help prevent DDoS attacks?
AI-driven systems analyze traffic behavior across multiple signals such as request patterns, IP reputation, and timing. Consequently, they can distinguish legitimate traffic spikes from malicious floods and automatically mitigate attacks without disrupting real users.
Is traditional antivirus still necessary in modern hosting security?
Yes, but primarily as a secondary layer. While antivirus tools catch known malware, behavioral analysis powered by AI detects advanced threats like polymorphic and fileless malware that signature scanning alone may miss.
What is predictive threat intelligence in hosting security?
Predictive threat intelligence uses machine learning to combine internal server data with global threat feeds. As a result, hosting providers can anticipate potential attacks and activate defenses before an incident occurs.
Can AI cybersecurity systems work without human involvement?
Not entirely. Although AI automates detection and response, human experts remain essential for decision-making, investigation, and oversight, ensuring balanced and reliable security operations.
Why does infrastructure level security matter when choosing a hosting provider?
Because security built directly into hardware, networks, and server management reduces vulnerabilities at every layer. Consequently, providers with architecture-level protection offer stronger long-term defense than those relying on add-on security tools.







