Every moment of every day thousands of rogue automated password guessing bots scour the internet testing login page after login page and trying username after username and passwords combination in an attempt to find that one, single, account’s password. Attacks that used to be little more than cannon fire in the dark are now able, increasingly, to capitalize on A.I., giant botnets and behavior homogeny to try and outwit traditional defenses. Consequently, conventional security measures aren’t enough to cope with today’s brute force attacks. In fact, as recently as the first few months of 2025, campaigns involving millions of IP addresses have been discovered targeting VPNs, firewalls and servers, a menacing reminder that modern brute force attacks are now well-oiled machines.
As a result, for hosting providers, this threat scales across entire infrastructures where one successful attack can breach systems at scale. As a result, pro-active monitoring and immediate response have transitioned from being nice to have protections to operational imperatives. If you’re unable to track attacks as they happen, then you’re going to encounter lost data, downtime, and a compromised reputation. That is why instant, automatic defense is essential. In this blog we will talk about how providers can identify brute-force attacks and terminate them in milliseconds using behavior analysis, machine learning, rate limiting and intrusion detection, through behavioral analysis, machine learning, rate limiting and intrusion detection to safeguard digital assets in a silent war that takes place around the clock.
Key Takeaways
- Continuous monitoring is essential. Regular updates and threat intelligence provides strong defenses against ever changing attacks.
- Real time detection is critical. Only at the speed of milliseconds, really a few but trusted ones inside millisecond. The attacks can be detected and stopped, before reaching exploits or data breach.
- AI improves accuracy. Machine learning captures sophisticated human-like attacks and reduces false positives.
- Layered security prevents failure. There are several layers of defense so even if an attack could happen, they can be stopped by one layer or another.
- Smart automation is necessary. Automation needs to be quick, but accessible to the user.
Your website deserves a faster and more secure web host.
Come aboard with UltaHost and experience the power of edge-enabled web hosting.
Understanding the Anatomy of Modern Brute Force Attacks
Before diving into detection mechanisms, it is important to first understand the nature of the threat itself. Take brute force attacks like automated, password cracking bots using leaked data combined with smart distribution to break into weak passwords at a faster, quieter rate than before.
Some of the most prevalent brute force attack are:
1 Simple Brute Force Attacks
Attackers systematically test every possible password combination.
- Easy to detect due to repeated failures from one source
- Can attempt thousands to millions of guesses per second
- Effective against short or weak passwords
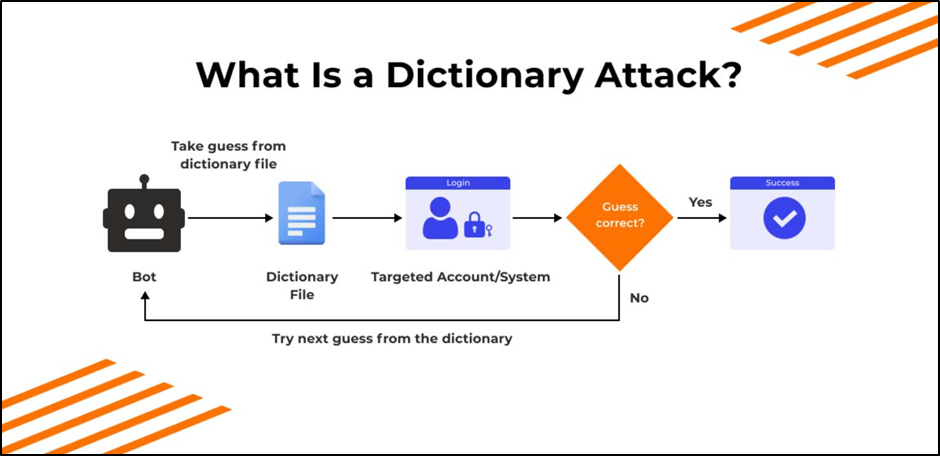
2 Dictionary Attacks
These use massive lists of real, commonly used passwords and leaked credentials.
- Can succeed quickly before basic alerts are triggered
- Targets popular passwords like “password123” or “admin”
- Exploits widespread password reuse
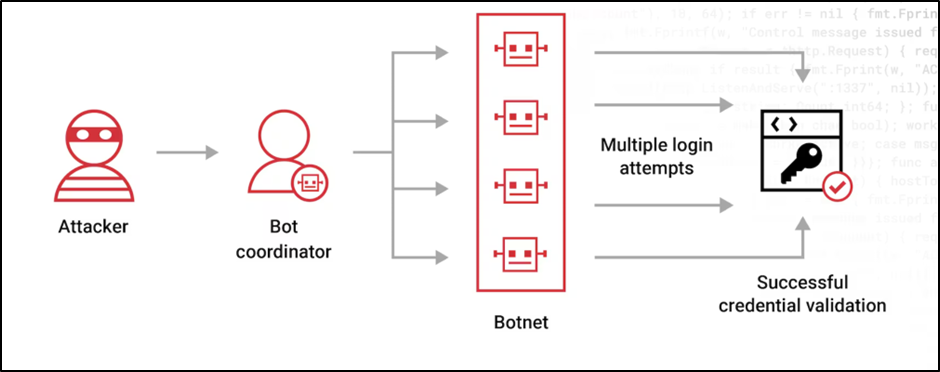
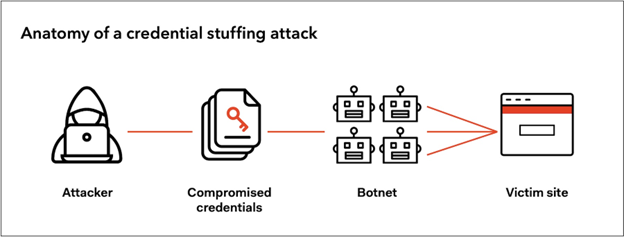
3 Credential Stuffing
Uses stolen username or password pairs from past data breaches.
- No guessing required credentials are already valid
- Works because over 60% of users reuse passwords
- Hard to detect since logins often succeed
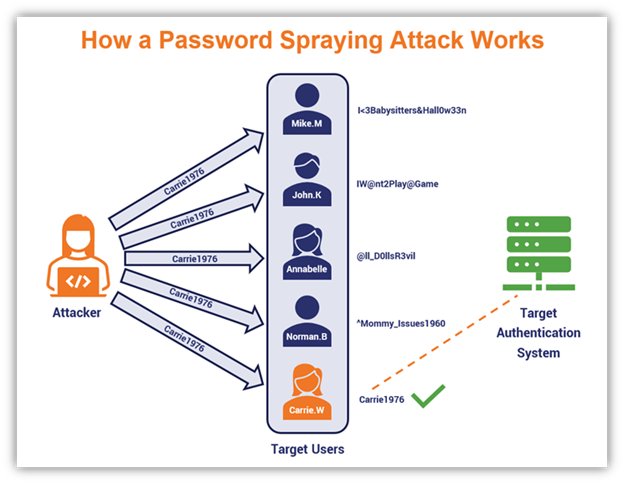
4 Password Spraying
Try one common password across many accounts.
- Requires system wide pattern analysis to detect
- Avoids triggering account based lockouts
- Each user sees minimal failed attempts
| It is important to know these types of attacks because each one leaves behind different digital fingerprints. Effectively defending from such threats often requires the detection of these patterns as they occur, and long before weak passwords have been compromised at scale. |
Real Time Detection Mechanisms: The First Line of Defense
Due to the speed of contemporary attacks, immediate response to dubious behavior is our most important defensive capability.Therefore, real-time detection mechanisms are the first and most important line of defense today. In today’s date, systems scrutinize login activity, traffic on the network and user behavior within milliseconds to maintain a balance between quick response to threats and allowing legitimate users.
1 Behavioral Analysis and UEBA
Behavioral analysis has become the gold standard in identifying sophisticated brute forces. With User and Entity Behavior Analytics (UBA), hosting services set up a baseline for regular behavior and alert on anomalies.
Key signals include:
- Typical login times and locations
- Common devices and networks
- Login speed and interaction patterns
- Historical user behavior
2 Rate Limiting and Threshold Monitoring
In addition to the behavioral analysis, an initial line of defense is rate limiting, controlling how many times users can try logins.
Modern implementations include:
- Multi-dimensional monitoring looks at multiple factors at once (so-called logs or login-related activity) that could factor into the IP, user name, session behavior and even subnet range or autonomous system number (ASN). Because of this, security systems can detect large-scale coordinated attacks even if the individual sources seem to be behaving normally.
- By default, basic rate limiting is enabled to limit the number of times a given IP address can attempt to log in. Although quite successful for simple attacks, it can be evaded in the case of large distributed botnets used by the attackers.
- Progressive rate limiting introduces increasing delays after each failed login attempt. It is a shot in the dark with each new failure adding time to it, making large scale attacks slower and less feasible.
| As a result, behavioral analysis and multi-layered rate limiting work together to catch coordinated attacks early preventing both fast moving threats and slow, methodical hijinks without damaging legitimate traffic. |
Machine Learning and AI Powered Attack Prevention
AI and ML have changed brute force from static, rule bound systems into adaptive defenses that constantly learn from both new attacks and user behavior, thereby being able to respond quickly as threats become more sophisticated.
1 How AI and Machine Learning Enhance Detection
Machine learning systems sort through the vast troves of authentication data in real time for anomalies that are too complex for humans and simple tools to distill.
Key capabilities include:
Advanced Pattern Recognition
- Login frequency and failure rates
- Geographic and time based activity
- User agents and browser fingerprints
- TLS and HTTP header characteristics
- Network and proxy behavior
Bot vs Human Differentiation
- Unnatural timing distributions
- Repeated rare header combinations
- Patterns inconsistent with human behavior
High Accuracy at Scale
- Billions of thwarted brute force attacks each year
- False positive rates below 0.01%
- Minimal disruption to legitimate users
Real Time and Predictive Defense
- Block the request
- Allow access
- Request additional verification
| Rely on AI-powered detection for a high performing implementation that offers speed, agility, and profound pattern analysis to keep all sorts of brute force attacks at bay before bad actors even know they are discovered. |
Network Level Detection and Infrastructure Security
Application level detection looks at user behaviour and login patterns, network level detection analyses traffic across the infrastructure to prevent malicious activity at the perimeter, protecting server resources and reducing the attack surface.
1 Key Network Level Detection Techniques
Intrusion Detection and Prevention Systems (IDS/IPS)
- Use deep packet inspection and stateful analysis
- Detect coordinated botnet activity across multiple servers
- Identify attack patterns invisible in individual server logs
Flow-Based Monitoring (IPFIX and Similar Technologies)
- Tracks short lived and repeated connections
- Highlights distributed login attempts across servers
- Enables automated blocking and rate limiting at routers and firewalls
Geographic and IP Reputation Analysis
- Maintains databases of known malicious IP ranges and proxies
- Flags traffic from botnet-linked or high-risk networks
- Supports geographic access controls for sensitive interfaces
DDoS Protection Systems
- Apply targeted controls like CAPTCHAs and endpoint rate limiting
- Analyze request types and destinations
- Distinguish brute force campaigns from traffic floods

| Improve your first line of defense by profiling traffic, flow and IP reputation in order to mitigate distributed brute force attacks before they reach applications. |
UltaHost’s Multi-Layered Brute Force Defense Architecture
To bootstrap protection against ever more complex brute force attacks, UltaHost employs a layered “defense in depth” approach to security, and rather than relying on just one via solution at a time. For one, at the network level, intelligent DDoS protection prevents malignant traffic from hitting your server in the first place. Meanwhile, its built-in ARM technology silently monitors activity behind the scenes as an always active detection layer. In addition, two factor authentication (2FA) provides an extra layer of verification and kicks in automatically when suspicious login activity is detected, even for accounts that don’t use 2FA by default. These safeguards ensure stable performance and enable UltaHost to uphold its 99.99% uptime guarantee, even when active attacks are underway.
In addition to perimeter defense, UltaHost enhances security with BitNinja as a defense option, which continuously checks login attempts and attack downgrades across the network to thwart attackers in real time. Its innovative suspicious login detection mechanism automatically score the risk of a login based on IP reputation, location mismatch, and various other factors such as devices being used, and behaviour. Additionally, this allows customers to restrict administrative access to trusted locations only, eliminating external brute force risks. Together with continuous monitoring and regular security audits, these integrated protections create a resilient environment where customer data and websites remain secure around the clock
Automated Response Systems and Real Time Mitigation
Today’s hosting providers all have automated systems that respond in milliseconds which means brute force attacks get stopped the moment they start and real users can continue to work as usual.
1 Key Automated Response Mechanisms
Adaptive Account Lockouts
- Allow more attempts from trusted, familiar locations
- Lock faster when activity shows bot-like behavior
- Increase lockout duration with repeated failures
Real-Time User Notifications
- Provide attack source and attempt details
- Encourage proactive password changes
- Improve transparency and trust
- Allow customizable alert preferences
Web Application Firewall (WAF) Integration
- Trigger CAPTCHAs and rate limits
- Block suspicious login tools and agents
- Protect vulnerable endpoints like WordPress login pages
- Prevent abuse without affecting site performance
Why Hosting Providers Can No Longer Afford to Wait
In cybersecurity, one of the most undervalued facts is that timing is everything. When a brute force campaign starts, attackers don’t stop and wait for defenders to catch up. As a result, even a brief pause in detection could determine whether an inbound intrusion attempt is blocked or a full blown data breach occurs.
The stakes are even higher for hosting providers specifically when they are for individual businesses. Not only do they control hundreds or thousands of websites from one place, but a single breached account can be a gateway into neighboring systems.
Moreover, the reputational damage that follows a breach is often more lasting than the breach itself. Clients trust their hosting provider to be the last line of defense, and once that trust is broken, it is extremely difficult to rebuild. As a result, investing in proactive, real time defenses is not just a technical decision, it is a business critical one.
Additionally, compliance requirements continue to get more stringent overall. GDPR in Europe, HIPAA in healthcare or PCI-DSS in financial services are just a few examples of regulations which require organizations to show they take an active and documented approach to prevent unauthorized access. As a result, hosting providers who have not yet utilized automated, intelligent defenses are putting their clients at risk and exposing themselves to legitimate cause of action and liability for damages.
In summary, the window for attackers is tight, but so is that of defenders. So, the only way is a method that leverages speed, intelligence and continual awareness.
Building a Culture of Security Across Teams
Technology alone, as impressive a tool as it is, cannot be enough on its own. The human factor, however, is often neglected, even the most advanced detection systems are rendered ineffective when they overlook it.
For the most part, teams need to be trained regularly on the latest attack patterns and response protocols. Brute force tactics learn and change, so training that was appropriate a year ago may not be adequate today. Cross functional awareness matters just as much, if not more than technical expertise.
Training alone is not enough, there needs to be definitive ownership of security responsibilities. When something goes awry, every minute matters. Without clear ownership, however, teams may make the mistake of believing that someone else is dealing with it. To prevent this from happening, organizations must have established roles related to threat detection, incident response and post incident analysis ahead of time.
Last, but not least, transparency with clients is an integral part of the security story. When clients know which protections are in place and how incidents are addressed, they’re more likely to take recommended security precautions on their end, like enabling two factor authentication or ensuring software remains up to date. Ultimately, a knowledgeable client is an active and required participant in the defense strategy not by any means a passive recipient of it.
The Evolution of Brute Force Defense: Looking Forward
As attackers and defenders adopt increasingly advanced technologies, brute force protection is rapidly evolving. Understanding these emerging trends helps organizations ensure their hosting providers are ready for next generation threats.
1 Key Trends Shaping the Future of Brute Force Defense
AI Powered Attacks and Defenses
- By continuously learning from real world attack patterns, these defenses become far more effective than traditional wordlists.
- Reflect real human password habits
- In response to these increasingly sophisticated attacks, equally advanced ML-based defenses are required to continuously retrain on new attack patterns.
Passwordless Authentication
- Based on WebAuthn standards
- Reduce brute force attack surface.
- Adoption will be gradual due to legacy systems
Zero Trust Security Models
- Monitors behavior even after login
- Restricts access when activity looks abnormal
- Limits the value of stolen credentials
Post-Quantum Security Preparation
- Could make traditional cracking extremely fast
- Driving research into quantum resistant cryptography
- Requires long term migration planning
From A Digital Security Standpoint:
Security systems driven by AI examine traffic anomalies, login patterns, and device usage in real time to detect brute force attacks before an account gets compromised. It has a side effect of reducing false positives, and at the same time makes it safe for real users to use their accounts.

Final Thoughts
Hacking a password will no longer be merely a simple guess work; it’s become intelligent, distributed and self adapting threat. As this blog has illustrated, successful defense relies on real time detection, AI-based analysis, layered security and automated response that work in concert to prevent attacks before they are carried out. Organizations can protect their data, keep the lights on, and remain resilient through an evolving digital landscape by selecting hosting providers who dedicate resources to next-generation monitoring, behavioral intelligence and security innovation.
Don’t let sluggish load times harm your business.
Host your website on UltaHost’s edge hosting with speed, security and reliability.
FAQs
How do hosting providers detect brute force attacks in real time?
Providers use behavioral analysis, machine learning, network monitoring, and rate limiting to identify suspicious login patterns within milliseconds.
What role does artificial intelligence play in brute force protection?
AI analyzes large volumes of login data to detect complex and human-like attack patterns, reducing false positives while improving detection accuracy.
What should website owners do to protect themselves?
Website owners should use strong passwords, enable 2FA, monitor account activity, keep software updated, and choose hosting providers with advanced security systems.
Will passwordless authentication eliminate brute force attacks?
Passwordless methods like passkeys and biometrics can greatly reduce brute force risks, but full adoption will take time due to legacy systems.
Can legitimate users be blocked by security systems?
Advanced systems are designed to minimize false positives, but temporary blocks may happen. Adaptive controls and user alerts help reduce inconvenience.








