Our teams are always busy developing and upgrading our security systems to entertain our customer’s security concerns more efficiently.
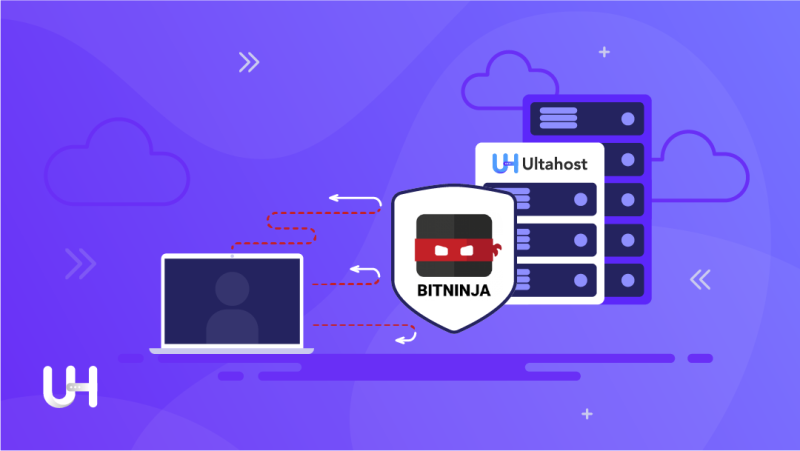
Thus, we are super excited to announce that we have deployed an unbreakable and most advanced security system within our servers, by keeping BitNinja on the channel as our Security Partner. And now, all our customers are super protected with BitNinja’s advanced security system, allowing them to create websites and blogs with further peace of mind.
Our servers have 99.99% uptime means our systems have maximum uptime because we are using highly secure, efficient, and upgraded systems, we are using BulletProof security system, because of BitNinja security algorithms. It is almost impossible to hack or send multiple requests at the same time to make it down.
When UltaHost claim that our customer will face the least security concerns and challenges, most of the layman’s few computing experts take this stance, just as a statement or market attraction strategical tagline.
By pointing out this issue, we just want to assure our customers and even those who are planning to switch to UltaHost, that it was just not a statement, in fact, this is true because we are using the most updated and efficient security of current time. And I will ensure it is very flexible and easy to use. And all that happened only because of BitNinja security.
What is BitNinja and how does it work?
BitNinja is a Security as a Service, server-side defense software. Mainly designed and built to protect the server from multiple threats with the least contribution from you and made you free from server maintenance and forensic security tensions. BitNinja is a self-learner powerful tool, who did its job silently in the dark without disturbing Users’ or servers’ processes like a Ninja.
BitNinja Working Model:
Its framework has been designed over Machine Learning Technology. It can upgrade itself after analyzing the attacks from multiple bots and then use that prior knowledge to create a shield for all deployed servers. In short, if BitNinja fights against one attack once, next time BitNinja will be updated and ready to give shut up to it. BitNinja is like a front-row passionate volunteer army, which fights against hackers, botnets, attackers, and malicious activities.
BitNinja Framework:
It is developed over a Machine Learning framework and uses Machine Learning algorithms to educate itself if some new type of attack is attacked over it. BitNinja algorithms start analyzing attackers’ algorithms, and after their analysis, they start educating their systems and updating their security over entire servers.
BitNinja Efficiency:
If we discuss BitNinja’s efficiency, it is highly effective and efficient. Moreover, it works silently because of which severe performance was not affected. It unbound you from daily, and weekly reports checking and making sure no malware, Bots, or attacks have been attached over the server. It works as an anti-bacterial soap against every attack. Just point out the vulnerabilities and auto-fix them all. It is an unbreakable shield against every attack. And make sure that the server won’t go down.
Benefits of BitNinja:
Another benefit of BitNinja is that it is a single-suit solution for multiple server problems and that one system is capable of addressing numerous server-side challenges.
Because of this, a user won’t have to configure various software’s on the server for every dedicated challenge. This saves cost, space within the secondary storage, computing resources, processes, human workforce used to maintain all those software’s, and maintenance cost, which ultimately decreases to economic and processes value.
However, it is a one-person army against every type of server attack. And it is easy to configure, deploy and maintain. It is almost compatible with every kind and specification of the server.
BitNinja Modules:
For this, they divide their security processes into 3 major categories and multiple subcategories. These are as follows:
- General Modules
- Detection Modules
- Captcha Modules
General Modules:
General Modules details are as follows:
- CLI: It contains a mandatory source code for BitNinja.
- Data Provider: It has to send scheduled and regular updates about the server to BitNinja central. Data like system resource usage, memory usage, system load, and BitNinja protection efficiency, are sent for statistical purposes.
- Shogun: It has to accept and forward security incidents time by time.
- System: It has to manage to license, and update the client’s servers’ security algorithms, and accept commands from BitNinja to enable or disable the WAF module.
- SSL Terminating: It has to unload HTTP’s connection and helps Captcha, HTTP & WAF module to work accurately.
- Proxy Filter: Although BitNinja blocks proxies over the system, this module is to enable trusted brokers to access the system.
- IP reputation Filtering Mode: It is a highly intelligent Botnet system, which detects malicious IPs and restricts their activities to limit the risk. Even it will block their activities if needed. It not only hinders their activities but also prevents infected systems from connecting to the network. It works in such a secret way that you are even not able to judge.
Detection Modules:
Detection modules details are as follows:
- AntiFlood: This module is like a Spiral Cord of the human body. It has to take information from all other modules and transmit it to the modules which need it. Moreover, its duty includes preventing attackers from harming your system.
- Out Bound Web Application Firewall (WAF): This module detects, and scans outgoing connections traffic in Realtime. If it found any suspicious connection, it sends the log to BitNinja central hub and tries to find which process and script are responsible for it. Furthermore, it may block that script or raise an alert.
- Defense Robot: The module waits for the information coming from the Malware Detection module. After receiving the data from it, it tries to find log lines related to the malware upload within the configured window.
- Web Honey Pots: When the hacker attacks your website, it will collect the attack data and block the attack & attacker’s IP. Even it will stop the gateway through which hacker enters the system.
- Port HoneyPot: This module will identify on the off chance that somebody does a profound port output on your worker (aside from syn secrecy sweep and some others). The module will likewise catch any traffic on these honeypots and answer to the solicitations, so when the assailant attempts to misuse one of these phony administrations, it will create episodes. It is an extremely successful approach to get at an early stage both direct assaults and botnet exercises.
- Log Analysis: It is responsible for analyzing log files on runtime and takes mandatory action if any suspicious activity was detected.
- DDOS attack detection: Network supervising module that can defeat excessive malicious traffic to prevent DoS attacks.
- Malware detection: Updated malware detection technologies are combined with standard methods to help in increasing the efficiency of malicious object detection and support proactive protection against new hostile programs.
- The Web Application Firewall (WAF): This module protects our client’s websites from a variety of common attacks like SQL injection, cross-site scripting, data thefts, or buffer overflowing. WAF monitors, filters, and blocks incoming malicious traffic on the website in real time.
The Captcha Module:
The idea of driving this module is really what makes BitNinja extraordinary. The framework screens and keeps up a notoriety information base of more than 4 million IPs in real time. This notoriety depends on the history of every IP action to forestall bogus lively squares with its 4-level notoriety positioning:
- Captcha HTTP Module: It is to authorize doubtful IPs of BitNinja database of Grey List and allow human web users to remove themself from the grey list by small authorization.
- Captcha Smtp Module: It is used to identify the false positives on the BitNinja grey list and removes human users from the grey list. (It will remove them automatically after monitoring their activities over the server)
- Captcha Ftp Module: This module will check the IP addresses that try to connect to it and detect if the IP is on the BitNinja grey list. If the IP is in the grey list, it will simulate the FTP connection and won’t allow any real FTP operations for the malicious IP.
Because of BitNinja’s outstanding services, we claim that we have 99.99% uptime. We have bulletproof security; our servers are highly efficient and have been giving remarkable services. And our customers have the least security concerns, and we have almost minimal server service and server maintenance issues and tickets.
If you enjoyed this article, then you’ll love the UltaHost hosting platform. Get 24/7 support from our support team. Our powered infrastructure focuses on auto-scaling, performance, and security. Let us show you the Kinsta difference! Check out our plans