Every time a customer enters their details on your website, they’re trusting you. They believe their data will not be used for malicious purposes. That trust is your most valuable business asset — and it’s encryption that will help you guard that trust.
Data encryption: switching comprehensible data into a mindless format. Only party who have the decryption key are able to read it. Encryption is not an optional extra in the modern hosting platform. It is the baseline requirement to run a credible, secure online business.
But here’s the thing. Most business owners understand encryption is important. Hardly anyone knows how it works in a hosting environment, where does it apply and what happens when its missing. That gulf in understanding poses real risk — to your business and your customers.
But here’s the thing. Most business owners understand encryption is important. Hardly anyone knows how it works in a hosting environment, where does it apply and what happens when its missing. That gulf in understanding poses real risk — to your business and your customers.
Key Takeaways
- SSL certificates form the backbone of encryption for any user data-centric web app.
- It is a definitive security risk — unencrypted hosting environments put businesses at risk for breaches, regulatory fines and reputational damage.
- End-to-end encryption protects the data between sending it from a user’s device to where the data is stored.
- Encryption is a critical compliance requirement for GDPR, HIPAA, PCI DSS and other major regulations.
- The encryption capabilities of your hosting provider are directly related to how protected your business data really is.
Not sure which hosting plan is right for your business?
Explore UltaHost’s full range of plans, built for speed, security, and real growth.
Why Data Encryption Can’t Be an Afterthought
Let us first address the business reality. Globally, the estimate of cybercrime could reach almost $10 trillion per year. One being that as digital systems expand, cybercriminals exploit vulnerabilities in sensitive information. In a majority of cases, attackers gain access to unencrypted or inadequately encrypted data and can steal and use it for financial crime or fraud.
The impact on businesses is more than just a loss of revenue. This leaves regulatory investigations in its wake for a single data breach. Under frameworks like GDPR, it can lead to huge fines. It can irreparably harm customer relationships developed over years. In addition, today’s consumers are far more conscious of data privacy.
So encryption is more than a technical safeguard. It’s a business signal. It communicates to customers, partners and regulators that you act thoughtfully. And in competitive markets, that signaling is important.
What Hosting Data Encryption Really Is
Host encryption isn’t some single switch you throw. It’s a layered system that secures data at various points in its life cycle. Knowing those stages will enable you to ask the right questions of your hosting provider.
Encryption in Transit
This is the most apparent layer of encryption. It secures data while traveling between a user’s browser and your server. Whether someone submits a form, pays for something or logs in to your site — that data is transferred over the internet. Not encrypted, can be sniffed.”
This is, from a business perspective, not negotiable. Non-HTTPS sites are penalized in Google search rankings. Browsers will mark them as “Not Secure.” Customers abandon them. So what is the cost of not having SSL? Lost traffic, lost trust and lost revenue.
Encryption at Rest
Data at rest is stored data that can apply to files on your server, database records, backups, logs etc. Encryption at rest means that even in the worst case if someone gets access to your storage — it will matter little since the data will not be of any use without decrypting it using key.
The last layer is of course very important for any hosting environment. Encryption at rest is what will be between an attacker and your customers information in case your server is compromised.
Most of the businesses think their hosting provider gets this done on their behalf automatically. That assumption is dangerous.
Database Encryption
Your database is responsible for more than just file storage — it contains your most sensitive information. Customer records, order histories, login credentials, personal details — it all lives there.
This data has a particular layer of protection around it with encryption at the database level. Encrypted fields are still safe even if someone breaks into your database.
This layer is especially critical if you have an ecommerce business. Attackers, in many cases, target payment information and addresses stored within databases as well as personal information.
End-to-End Encryption
End-to-end encryption (E2EE) is an ideal. It guarantees that data is encrypted when it leaves the sender and until what they intended receiver decrypts it. No one in between — not even the hosting provider, it means, can read it.
E2EE is especially critical for messaging platforms, health services, and any service processing delicate personal communications. As expectations of data privacy increase, more hosting environments are implementing E2EE as a standard offering.]
The Encryption Standards That Matter, Actually
Not all encryption is equal. The protection this offers in practice depends on the standard used. Here are the major ones businesses need to know about.
AES-256: Advanced Encryption Standard using a 256 bit key. Just one of the most phenomenal standards for encryption at rest. It is used by governments, banks, and premium hosting providers around the world. With modern technology, brute-forcing AES-256 is practically impossible.
TLS 1.3: The newest version of Transport Layer Security It’s faster and far more secure than its predecessors.
RSA & ECC: These are asymmetric cryptographic algorithms that are leveraged in SSL/TLS certificate processes. Integration of ECC (Elliptic Curve Cryptography) give equivalent security to RSA but much smaller key sizes — hence faster performance without any compromise in the protection.
To assess your hosting provider, ask them specifically which standards are in use. “I want a clear answer: ‘we use encryption’ is not enough. You need details — because your regulatory obligations depend on them.
Encryption and Regulatory Compliance
Here’s where encryption becomes a business liability. Note: Most major data protection regulations mandate encryption at a control level.
GDPR: The General Data Protection Regulation mandates that businesses processing personal data about European Union citizens — be it customers or employees — must take suitable technical measures to protect that data, with encryption being the most common. Not encrypting data can lead to a fine of €20 million or up to 4% annual global revenue.
Compliance with PCI DSS (Payment Card Industry Data Security Standard) that requires encryption of card data in-transit and at-rest. Without compliance, you could potentially lose your ability to process card payments altogether.
HIPAA: Encrypt private health information (PHI) for healthcare businesses. The financial and reputational blow that unencrypted PHI in a breach scenario will incur is enormous.
SOC 2: SOC 2 certification for SaaS and cloud businesses requires evidence of encryption controls throughout your environment.
Common Encryption Pitfalls in Hosting Environments
Knowing where things fail allows businesses to improve decision-making. Here are the most common encryption failures noticed in hosting environments.
Expired SSL Certificates
SSL certificates come with expiration dates. An expired certificate will cause encryption to break, and browsers will warn users. Visitors leave instantly. Revenue drops. Most hosting platforms offer auto-renewal these days — take it.
Mixed Content Errors
Occurs when an HTTPS page loads resources over HTTP. The page was encrypted but some portions are not. This leaves security gaps and browser warnings. This is a very typical problem after migrations.
Weak Cipher Suites
Even with SSL enabled, some legacy servers employ deprecated cipher suites. These have known vulnerabilities. These are exploitable by attackers to decrypt traffic. Your hosting provider should turn off weak ciphers and only support strong, modern ones.
No Encryption in Rest
Even though many hosting environments encrypt data while in transit, they store it unencrypted. Unencrypted stored data is immediately accessible if a server gets breached or a backup gets stolen.
Bad Key Management
The encryption is effective only to the extent that keys are kept secure. When keys for the encryption stored insecurely or not rotated regularly, the very encryption falls flat.
How Different Platforms Approach Encryption
Encryption itself has also advanced in how leading hosting platforms adapt, configure, and manage its implementation. This is what a hosting environment focused on modern security looks like.
Automatic SSL provisioning gives every site HTTPS by default. No manual certificate installation. No chance of failing to renew. Certificates are automatically issued, installed and renewed.
Any files stored on the platform automatically utilize server-side encryption. This provides a full at-rest encryption posture in conjunction with encrypted databases.
Constant Certificate Monitoring – Servers receive warnings about upcoming expiration, misconfigurations and SSL vulnerabilities before they become a threat to business operations.
UltaHost: Data Encryption is Our Top Priority
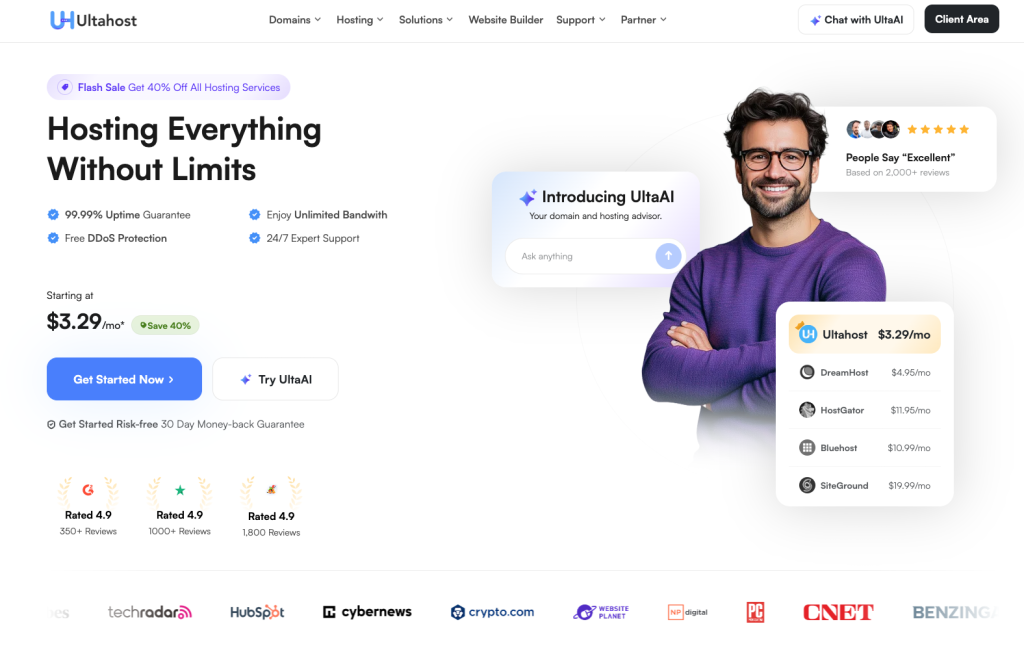
When fat stacks of data flow in and out of your business, the encryption capabilities of its hosting provider aren’t a trivial matter. They’re at the center of your whole security posture. UltaHost knows this — and it is clear in how their platform works.
All hosting plans by UltaHost come with free SSL certificates. All websites at UltaHost are available with a free SSL (HTTPS). It means no additional payments, no manual setup, and no danger of your certificate expiring unexpectedly.
But UltaHost’s commitment to encryption runs deeper than SSL. Your files, your databases, your backup copies — all safe.
In addition, UltaHost Managed VPS Hosting has set its server environments in a way to mitigate common encryption failures. Platform-level fixes mitigate mixed content issues, weak cipher suites, and outdated security configurations. You don’t need to be a security expert in order to enjoy expertise-level protection.
UltaHost’s WordPress Hosting encryption capabilities provide a firm technical base for compliance challenges, whether those obligations are with GDPR, PCI DSS, or HIPAA. This becomes more manageable if your hosting provider has baked the appropriate controls into the environment.
In a word, UltaHost thinks of encryption as infrastructure — not some extra feature. Because that is precisely what it is in the threat landscape of today.
How to Enhance Encryption in Your Hosting Environment
Even with a good hosting provider, there are things businesses should be actively doing.
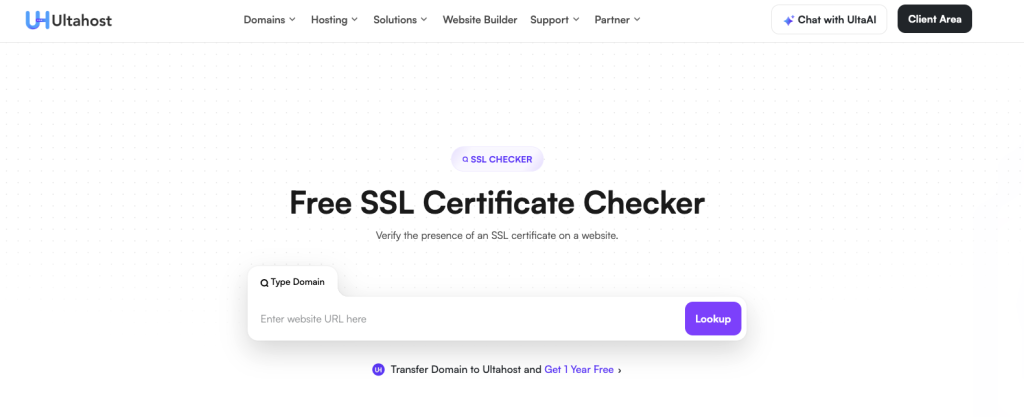
Audit your SSL configuration regularly. Use tools like SSL Labs’ SSL Test to verify your certificate strength, supported protocols and cipher suites. Do this at least quarterly.
Enable HSTS (HTTP Strict Transport Security). This tells browsers to always use HTTPS while browsing your site—even when someone types HTTP. It protects against downgrade attacks and strengthens your encryption posture.
Encrypt sensitive database fields individually. In addition, store sensitive information—such as passwords, payment tokens, and identity numbers—in an encrypted field to complement full-database encryption.
Rotate encryption keys periodically. Encryption keys must rotate frequently. Be sure your hosting provider can support key management.
Test your backups. Of course, encrypted backups are only useful as long as they can be decrypted and restored successfully. HPs itself for testing, the best way is to regularly test if your backup restoration process is working — not just the creation of backups.
Encryption should never be treated like a feature to be turned on or off from the infrastructure perspective. You need to architect it as a default architectural layer of the hosting environment. Choose hosting providers that automatically enforce encryption for data at rest, in transit, and within database systems.
When encryption isn’t merely a manual configuration, but part of the architecture of the platform itself, the risk of misconfiguration, expired certificates and weak protocols decreases dramatically.
Make Your Hosting GDPR-Compliant?
With Ultahost, get transparent data management, advanced encryption, and reliable hosting environments built for modern regulatory standards.
Conclusion
Trust in the digital economy enables customers to feel comfortable sharing sensitive information with your business. More importantly, it protects your systems when attackers inevitably test your environment. At the same time, it reassures regulators that your organization handles data responsibly.
Fortunately, modern hosting solutions have made robust encryption easier than at any other point in history, with built-in functionalities. However, a good hosting provider can do much of the technical heavy lifting for you. But it is still vital to know what your platform really does. More specifically, business owners need to know the potential security gaps and do what can be done to fill those in.
FAQs
My site doesn’t accept payments, so do I even need SSL?
Yes, absolutely. No harm in testing them on a dog to make sure they work safely — and someone with no initial idea who it is → where the choking starts happening in the process. Google also ranks HTTPS sites higher in search results.
What is the difference between SSL and TLS?
TLS (Transport Layer Security) is the upgraded version of SSL. Though SSL is the outdated old version of this protocol, and we don’t use that anymore as a term ever so commonly. When they refer to SSL these days, in reality what they mean is TLS. Just make sure your host supports TLS 1.2 or 1.3.
Will this slow my site down?
Modern encryption should not incur a noticeable performance cost. In fact, TLS 1.3 is faster than its predecessors. The benefits of running HTTPS from the perspective of both security and SEO massively outweigh any small overhead.
What will happen when I let my SSL certificate expire?
Visitors immediately encounter a security warning from their browsers. Users leave, traffic plummets. This is one of those time-consuming tasks that you’d never want to forget and one way to completely avoid this, use a hosting provider that has automatic renewal of SSL.
Does encrypting my records at rest affect how I search, or query for my database?
Recent Innovations in Database Encryption These cryptography methods enable queries to function normally while securing disk data in an encrypted format. When done correctly solutions will be barely noticeable in terms of performance..









